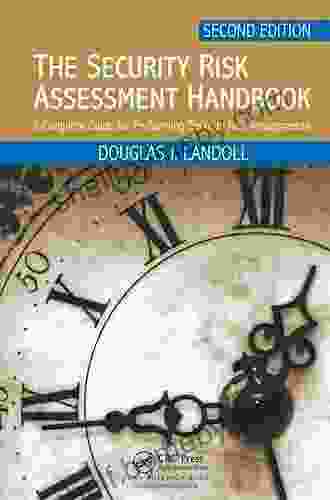
Complete Guide to Performing Security Risk Assessments: Protect Your Business from Cyber Threats

5 out of 5
| Language | : | English |
| File size | : | 18210 KB |
| Screen Reader | : | Supported |
| Print length | : | 432 pages |
In today's digital world, every business is vulnerable to cyber attacks. Data breaches, ransomware attacks, and other malicious activity can cause significant financial losses, reputational damage, and legal liability. To protect your business from these threats, it is essential to conduct regular security risk assessments.
A security risk assessment is a systematic process of identifying, analyzing, and evaluating the risks to your business's information assets. By understanding the risks you face, you can take steps to mitigate them and protect your business from cyber threats.
This comprehensive guide will provide you with everything you need to know about performing security risk assessments. We will cover the following topics:
- What is a security risk assessment?
- Why are security risk assessments important?
- How to perform a security risk assessment
- Common security risks
- How to mitigate security risks
What is a security risk assessment?
A security risk assessment is a systematic process of identifying, analyzing, and evaluating the risks to your business's information assets. The goal of a security risk assessment is to identify and prioritize the risks that pose the greatest threat to your business. Once you have identified and prioritized the risks, you can take steps to mitigate them and protect your business from cyber threats.
Why are security risk assessments important?
Security risk assessments are important because they help you to:
- Identify the risks to your business's information assets
- Prioritize the risks that pose the greatest threat to your business
- Take steps to mitigate the risks and protect your business from cyber threats
- Comply with regulations and industry standards
How to perform a security risk assessment
There are many different ways to perform a security risk assessment. The following steps provide a general overview of the process:
- Identify your business's information assets: The first step is to identify all of the information assets that are critical to your business. This may include data, applications, systems, and infrastructure.
- Identify the threats to your information assets: Once you have identified your information assets, you need to identify the threats that could potentially harm them. These threats may include cyber attacks, natural disasters, and human error.
- Analyze the risks: The next step is to analyze the risks to your information assets. This involves assessing the likelihood of each threat occurring and the potential impact of each threat if it does occur.
- Evaluate the risks: Once you have analyzed the risks, you need to evaluate them to determine which risks pose the greatest threat to your business. This involves considering the likelihood of each risk occurring, the potential impact of each risk if it does occur, and the cost of mitigating each risk.
- Mitigate the risks: The final step is to mitigate the risks that pose the greatest threat to your business. This may involve implementing security controls, such as firewalls, intrusion detection systems, and access control systems.
Common security risks
There are many different types of security risks that can threaten your business. The following are some of the most common:
- Cyber attacks: Cyber attacks are one of the most common security risks that businesses face. Cyber attacks can take many forms, including malware attacks, phishing attacks, and ransomware attacks.
- Natural disasters: Natural disasters, such as hurricanes, floods, and earthquakes, can also pose a significant threat to your business. Natural disasters can damage or destroy your IT infrastructure, which can lead to data loss and business disruption.
- Human error: Human error is another common source of security risks. Employees may accidentally delete data, give access to unauthorized users, or fall victim to phishing attacks.
How to mitigate security risks
There are many different ways to mitigate security risks. The following are some of the most effective:
- Implement security controls: Security controls are measures that you can put in place to protect your business from security risks. Security controls may include firewalls, intrusion detection systems, and access control systems.
- Educate your employees: One of the best ways to mitigate security risks is to educate your employees about the risks and how to protect themselves from them. Educate your employees about phishing scams, malware, and other security threats.
- Create a security plan: A security plan is a document that outlines your business's security policies and procedures. A security plan should include information about how to identify, analyze, and mitigate security risks.
Security risk assessments are an essential part of protecting your business from cyber threats. By understanding the risks you face, you can take steps to mitigate them and protect your business from financial losses, reputational damage, and legal liability.
If you are not sure how to perform a security risk assessment, you should consult with a qualified security professional. A security professional can help you to identify the risks to your business, analyze the risks, and develop a plan to mitigate the risks.
By taking the steps outlined in this guide, you can protect your business from cyber threats and ensure that your business is well-prepared to face any security challenges.
Free Download your copy of the Complete Guide for Performing Security Risk Assessments today!
Free Download Now
5 out of 5
| Language | : | English |
| File size | : | 18210 KB |
| Screen Reader | : | Supported |
| Print length | : | 432 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Mometrix
Mometrix Helen Greathead
Helen Greathead Jim Randel
Jim Randel Kent David Kelly
Kent David Kelly Rick Antonson
Rick Antonson Ronald Kessler
Ronald Kessler Vanessa Hua
Vanessa Hua Helen Cathcart
Helen Cathcart Jess Smith
Jess Smith Ilene Skeen
Ilene Skeen Howard Jackson
Howard Jackson Lily Nichols
Lily Nichols Ingrid P Wicken
Ingrid P Wicken John H Falk
John H Falk Madeleine Korbel Albright
Madeleine Korbel Albright Iasha King
Iasha King Hayley Campbell
Hayley Campbell Nick Marshall
Nick Marshall Rebecca Hall
Rebecca Hall Nigel Cumberland
Nigel Cumberland
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Stephen FosterEmbark on a Heartwarming Journey with "Hermie & Friends": A Timeless Tale...
Stephen FosterEmbark on a Heartwarming Journey with "Hermie & Friends": A Timeless Tale...
 Dylan MitchellEmpowering Medical Excellence: Introducing The Pocketbook For Paces Oxford...
Dylan MitchellEmpowering Medical Excellence: Introducing The Pocketbook For Paces Oxford...
 John SteinbeckOn Fertile Ground: Healing Infertility - Your Essential Guide to Hope and...
John SteinbeckOn Fertile Ground: Healing Infertility - Your Essential Guide to Hope and... Marcel ProustFollow ·17.2k
Marcel ProustFollow ·17.2k Roberto BolañoFollow ·2.2k
Roberto BolañoFollow ·2.2k Houston PowellFollow ·9.8k
Houston PowellFollow ·9.8k Dan BellFollow ·6.6k
Dan BellFollow ·6.6k Philip BellFollow ·8k
Philip BellFollow ·8k Shane BlairFollow ·3.1k
Shane BlairFollow ·3.1k Fabian MitchellFollow ·17.9k
Fabian MitchellFollow ·17.9k Lord ByronFollow ·10.5k
Lord ByronFollow ·10.5k
 Bo Cox
Bo CoxUncover the Enchanting Pearl of the Arabian Gulf: Insight...
Escape to the opulent...
 Michael Crichton
Michael CrichtonInsight Guides Pocket Baku Travel Guide Ebook: Your...
An Enchanting Journey...

 Eugene Scott
Eugene ScottLearn to Paint Scenic Scenes: Unveil the Secrets of...
Step into the...
 Benji Powell
Benji PowellEmbark on a Culinary Adventure with "The Ultimate Sichuan...
Sichuan cuisine,...
 Finn Cox
Finn CoxDiscover the Enchanting World of Art Nouveau: A...
Immerse yourself in the captivating beauty...
 Corey Green
Corey GreenUncover the Vibrant World of Guatemalan Chicken Buses: An...
Step into a world of vibrant colors,...
5 out of 5
| Language | : | English |
| File size | : | 18210 KB |
| Screen Reader | : | Supported |
| Print length | : | 432 pages |